Trips : How to Disable Windows Services in Windows 11
How to stop windows service in Windwos 11 [Step by Step]
09.12.2022 / Windows
In this guide, we will show you three different methods to disable and stop Services on your Windows 11 PC. Services are a part of the Microsoft Management Console (MMC) snap-in, and at a particular point in time, there are a plethora of such services concurrently running in the background. Each of them handles a specific task or application, without which the associated program might not function correctly. So if these services are of so much significance, why is there a need to disable or stop them?
Well, in some instances an app or software might not function along the expected lines and the root cause of the same could be linked to their particular service. To rectify this issue, you will either have to disable/re-enable their services or stop and then restart them. Likewise, in some cases, a third-party service might conflict with the other system apps and services and hence you might have to disable or stop those buggy services.
Moreover, some of the non-essential services are also known to hog excessive system resources, which leads to high CPU and RAM usage. So in all these scenarios, the best bet is to disable or stop these services on your Windows 11 PC. And in this guide, we will show you how to do just that using four different methods. These include the System Configuration, Services Menu, Task Manager, and Command Prompt. You may refer to the one that is in sync with your requirement.
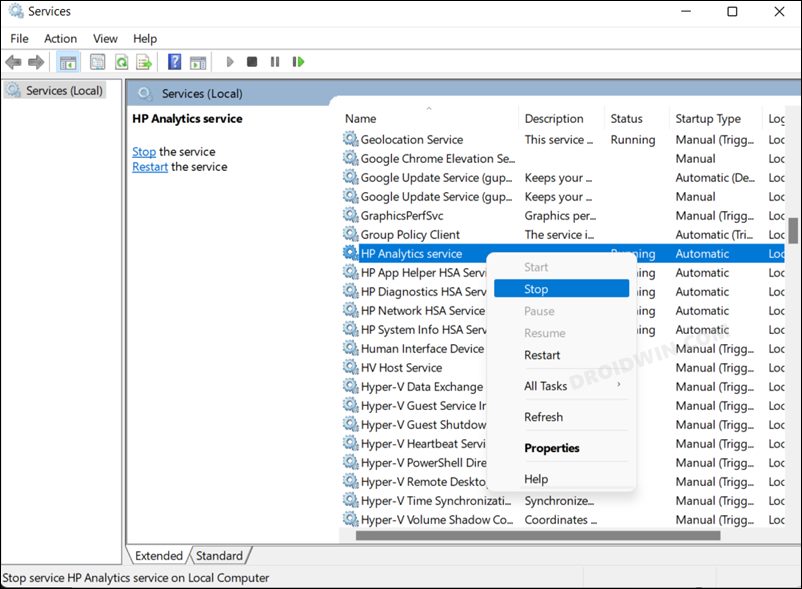
How to Stop Windows 11 Services via Services Menu
This is the most straightforward and well-known approach that is usually opted for by the users. One downside is that you will only be able to stop/start a service using this method, not disable/enable it. So on that note, let’s get started.
- Head over to the Start menu, search Services, and open it.
- Then scroll to the desired service, right-click on it, and select Stop.
- You could also select Properties from the context menu and then click Stop from the subsequent menu.
So these were the two different approaches to stop a service in Windows 11 via the Services app. If at any point in time, you wish to restart that service, just right-click on it and select Start. Or you could also right-click on it, select Properties and then click the Start button.
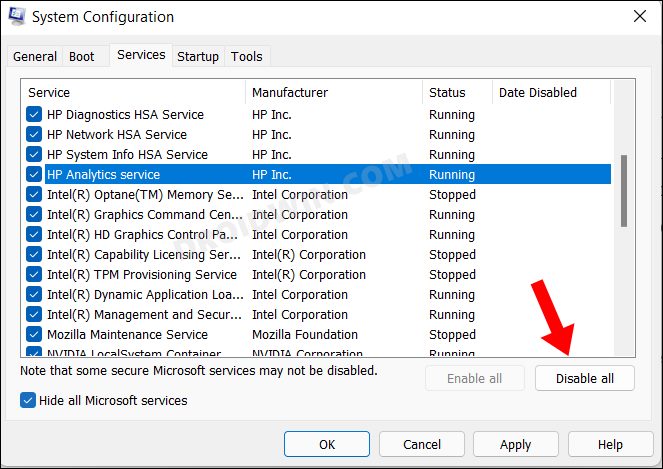
How to Disable Windows 11 Services via System Configuration
This method comes with two big advantages. First off, you could easily disable all the services with just a single click. Likewise, you could also disable all the non-Microsoft Services in just one click, without the need for manual segregation of Microsoft and non-Microsoft services. The downside? Well, it just allows you to disable services and not stop them. So if that’s well and good, then let’s get started.
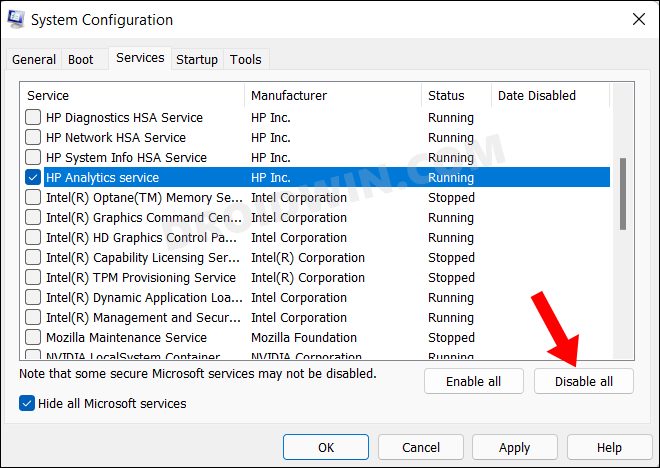
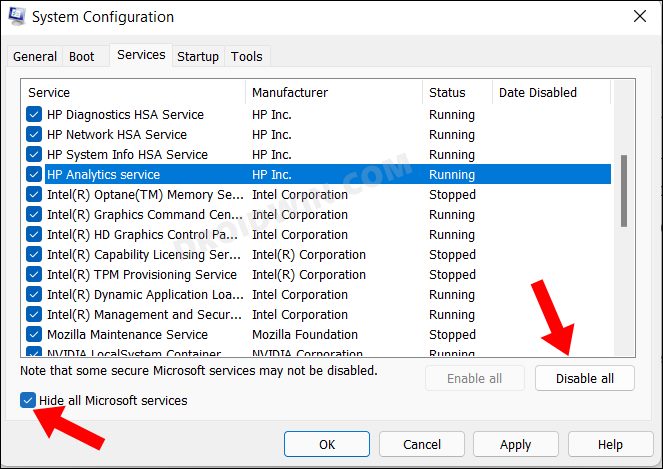
- Head over to the Start menu, search System Configuration, and open it.
- Then go to the Services tab and click on Disable All to disable all the services.
- If you wish to disable a single service, then uncheck all the other services and just leave the required service checkmark. Then click on Disable All and that particular service will be disabled.
- On the other hand, if you want to disable non-Microsoft Services, then click on Hide All Microsoft Services and then click on the Disable All button.
These were the steps to disable services in Windows 11 via the System Configuration menu. To enable any of the disabled services, just select the desired service/services and click on the Enable All button.
How to Stop Windows 11 Services Using Task Manager
This method is quite easy to execute but on the flip side, you will only be able to stop the services, not disable them. This is because its root lies in the Services menu (that we discussed in Method 1). So whatever drawback and perks this method has, it is the same as the one that the Services app has. So with that in mind, let’s check out this method:
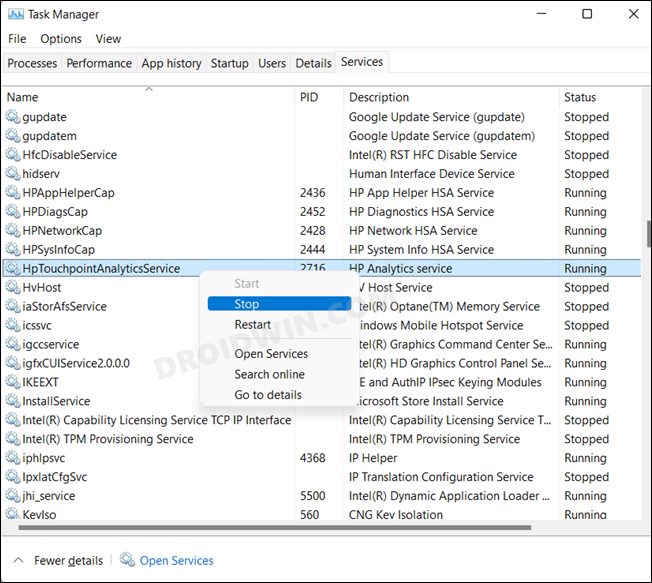
- Bring up the Task Manager via Ctrl+Shift+Esc shortcut keys.
- Then go to the Services tab, right-click on a particular service, and select Stop.
So this was the short and quick method to stop WIndows 11 services via Task Manager. If at any point in time, you wish to restart the service, then just right-click on the disabled service and select Start.
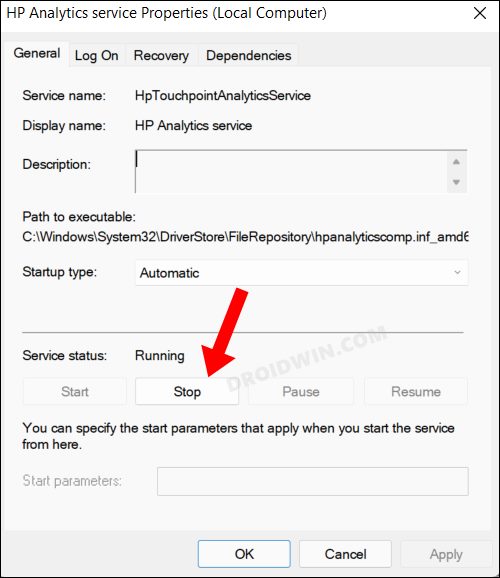
Stop and Disable Windows 11 Services Via Command Prompt
This is the only method out of the four that supports both the disabling and stopping of services. However, this method is also somewhat time-consuming and technical in nature. Keeping both these points in mind, let’s get started.
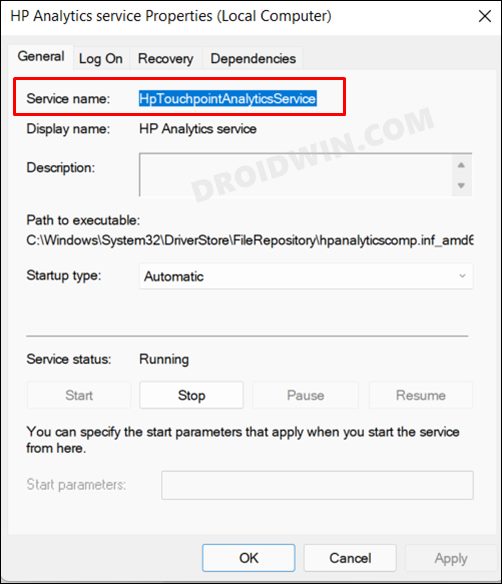
- First and foremost, you will have to get hold of the service name that you wish to disable or stop.
- For that, launch the Services menu, select the desired service, right-click on it and select Properties. Then note down the name next to Service Name.
- As for this guide, we will be taking HP Analytic Service as an example, having the service name HpTouchpointAnalyticsService.
- Moving on, head over to the Start Menu, search CMD and launch Command Prompt as an administrator.
- Now execute the required command given below, depending on whether you want to disable the service or stop it.
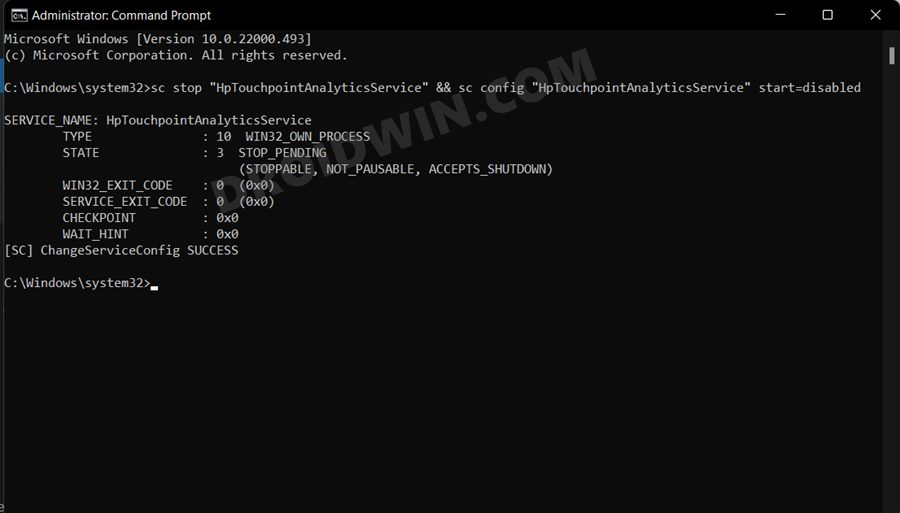
Disable Service via CMD
- Execute the below command in the CMD window to disable a service.sc stop „service name“ && sc config „service name“ start=disabled
- Make sure to replace the service name from the above command accordingly.
- For example, if we want to disable HP Analytic Service, then the command will transform to:sc stop „HpTouchpointAnalyticsService“ && sc config „HpTouchpointAnalyticsService“ start=disabled
Stop Service via CMD
- Execute the below command in the CMD window to disable a service.sc queryex Service Name
- Make sure to replace the service name from the above command accordingly.
- Taking HP Analytic Service as an example, the command in our vase will transform to:sc queryex HpTouchpointAnalyticsService
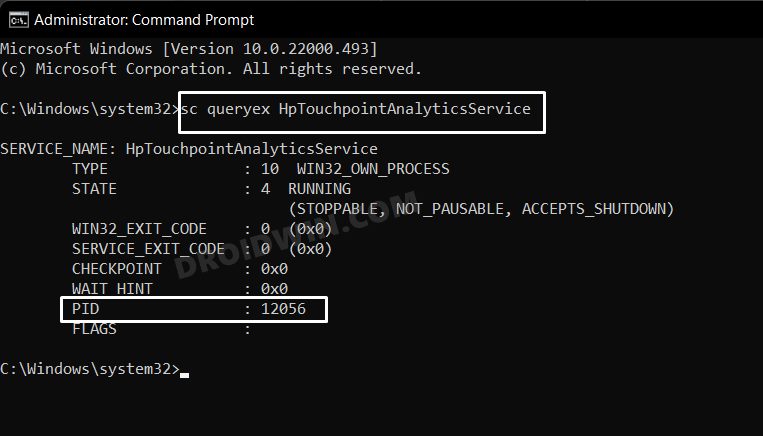
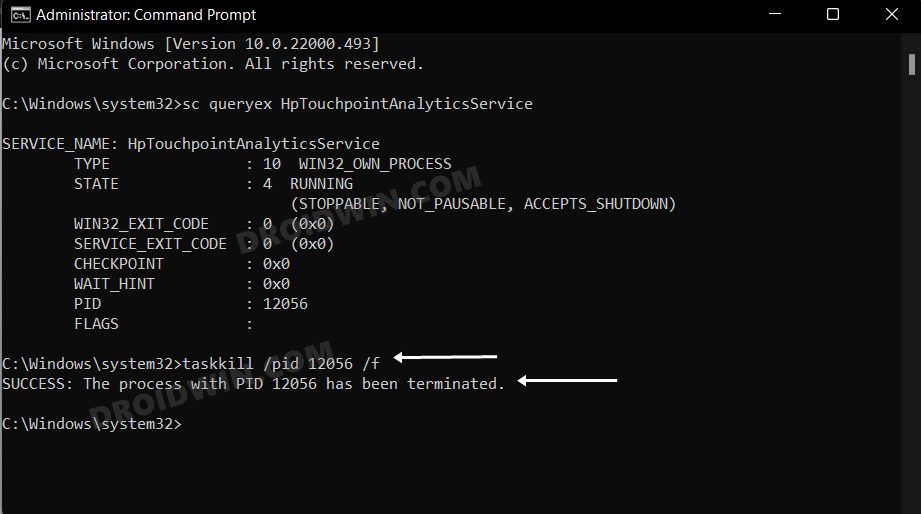
- Now note down the PID value and execute the below command [type in the OID value in place of xxxx]:taskkill /pid xxxx /f
- For example, the PID value in our case is 12056, so the command will be:taskkill /pid 12056 /f
So with this, we round off the guide on how you could disable and stop service in Windows 11. We have shared four different methods for the same. Do let us know which one you ultimately decided to settle for. Likewise, all your queries are welcomed in the comments section below.
